Breadcrumb
Semi-Fragile Watermark for the Authentication and Recovery of Tampered Images
In order to strengthen the safety of corporate multimedia assets, a semi-fragile watermarking method is developed, which makes use of the integer wavelet transform (IWT) and the discrete cosine transform (DCT) for tamper detection and recovery. In this paper, we produce two distinct kinds of watermarks: an authentication watermark and a recovery watermark. A tamper detection methodology is utilized at the receiving end to check the watermarked image for validity and detect any assaults. If the changes are determined to be malicious, the suggested tamper recovery method is used to restore the

Computational Intelligence for Medical Internet of Things (MIoT) Applications
Computational Intelligence for Medical Internet of Things (MIoT) Applications: Machine Intelligence Applications for IoT in Healthcare explores machine intelligence techniques necessary for effective MIoT research and practice, taking a practical approach for practitioners and students entering the field. This book investigates advanced concepts and applications in the MIoT field, guiding readers through emerging developments and future trends. A wide range of international authors guide readers through advanced concepts, including deep learning, neural network, and big data analytic
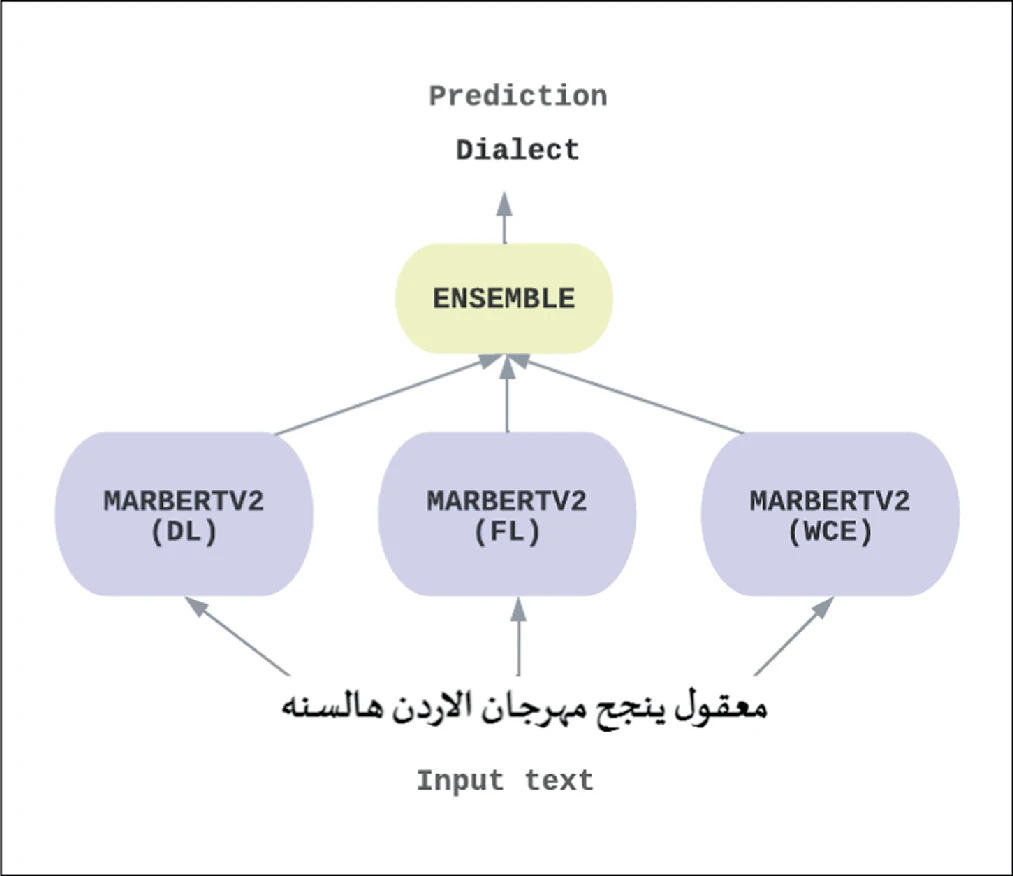
In the Identification of Arabic Dialects: A Loss Function Ensemble Learning Based-Approach
The automation of a system to accurately identify Arabic dialects many natural language processing tasks, including sentiment analysis, medical chatbots, Arabic speech recognition, machine translation, etc., will greatly benefit because it’s useful to understand the text’s dialect before performing different tasks to it. Different Arabic-speaking nations have adopted various dialects and writing systems. Most of the Arab countries understand modern standard Arabic (MSA), which is the native language of all other Arabic dialects. In this paper we propose a method for identifying Arabic dialects
NGU_CNLP at WANLP 2022 Shared Task: Propaganda Detection in Arabic
This paper presents the system developed by the NGU_CNLP team for addressing the shared task on Propaganda Detection in Arabic at WANLP 2022. The team participated in the shared tasks' two sub-tasks which are: 1) Propaganda technique identification in text and 2) Propaganda technique span identification. In the first sub-task the goal is to detect all employed propaganda techniques in some given piece of text out of a possible 17 different techniques, or to detect that no propaganda technique is being used in that piece of text. As such, this first sub task is a multi-label classification
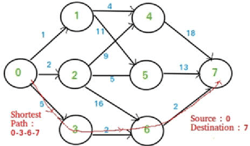
Comparison of Parallel and Serial Execution of Shortest Path Algorithms
Shortest Path Algorithms are an important set of algorithms in today's world. It has many applications like Traffic Consultation, Route Finding, and Network Design. It is essential for these applications to be fast and efficient as they mostly require real-Time execution. Sequential execution of shortest path algorithms for large graphs with many nodes is time-consuming. On the other hand, parallel execution can make these applications faster. In this paper, three popular shortest path algorithms-Dijkstra, Bellman-Ford, and Floyd Warshall-Are both implemented as serial and parallel programs
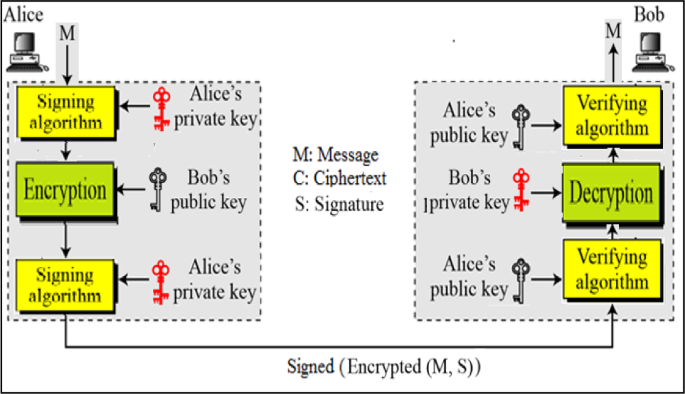
Networking and cryptography library with a non-repudiation flavor for blockchain
Blockchain is currently one of the most widely discussed inventions in the information and communication technology industry. It is a pillar of the fourth industrial revolution and it is a cryptographically demanding technology that is regarded as one of the most influential topics in academia. Many blockchain platforms currently utilize third-party cryptographic libraries that offer many cryptographic primitives in order to ensure users' protection against cyber-attacks. The Networking and Cryptography library (NaCl) is an open-source library for cryptographic primitives. NaCl is known to be
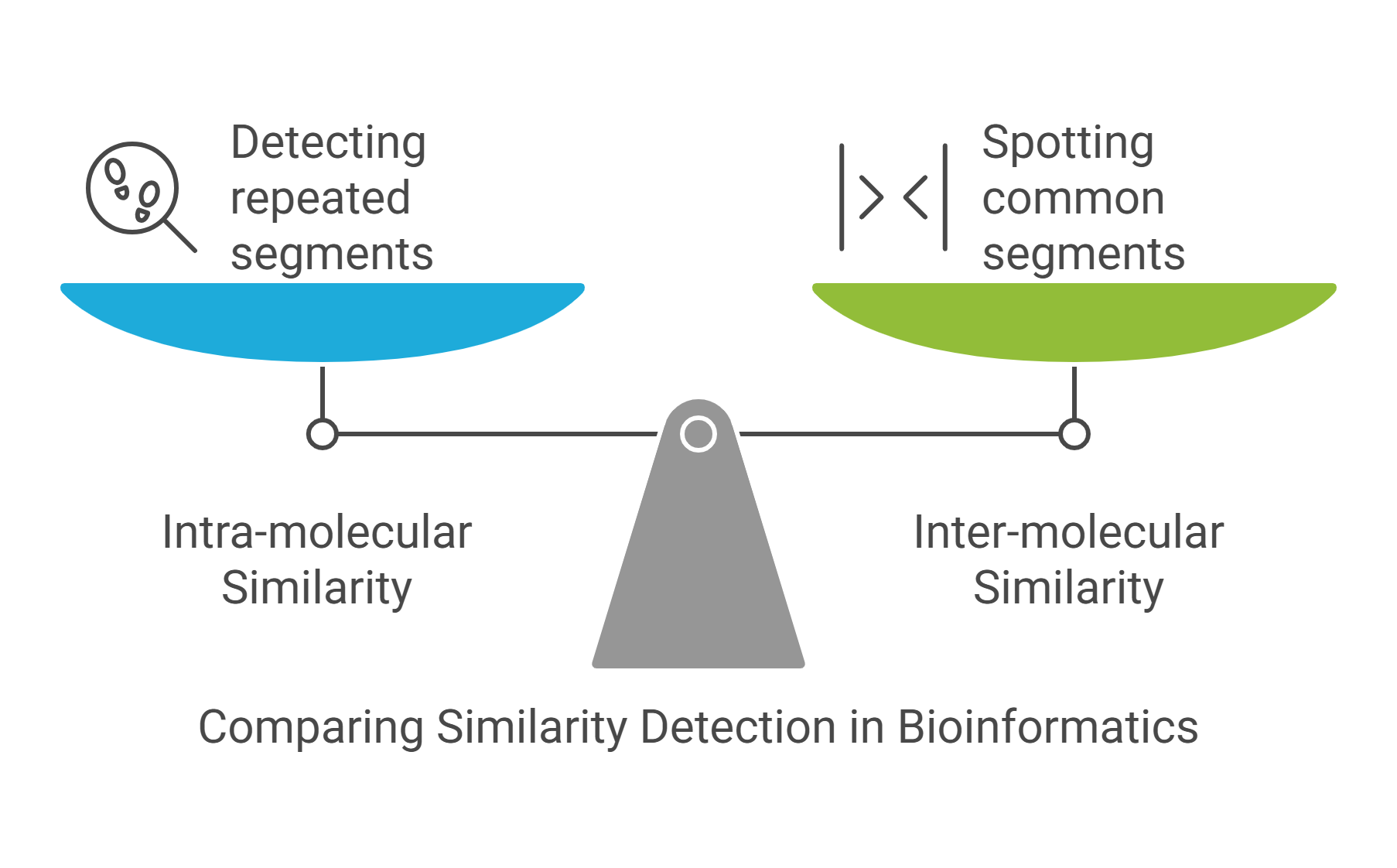
String mining in bioinformatics
Sequence analysis is a major area in bioinformatics encompassing the methods and techniques for studying the biological sequences, DNA, RNA, and proteins, on the linear structure level. The focus of this area is generally on the identification of intra-and inter-molecular similarities. Identifying intra-molecular similarities boils down to detecting repeated segments within a given sequence, while identifying inter-molecular similarities amounts to spotting common segments among two or multiple sequences. From a data mining point of view, sequence analysis is nothing but string-or pattern
Customer Churn Prediction Using Apriori Algorithm and Ensemble Learning
Customer churn poses a formidable challenge within the Telecom industry, as it can result in significant revenue losses. In this research, we conducted an extensive study aimed at developing a viable customer churn prediction method. Our method utilizes the Apriori algorithm's strength to identify the key causes of customer churn. In the pursuit of this goal, we utilized multiple machine learning predictive models. All of which were developed from the insights gleaned from the Apriori algorithm's feature extraction for churning customers. This extensive analysis encompassed a spectrum of
Comparison of Different Deep Learning Approaches to Arabic Sarcasm Detection
Irony and Sarcasm Detection (ISD) is a crucial task for many NLP applications, especially sentiment and opinion mining. It is also considered a challenging task even for humans. Several studies have focused on employing Deep Learning (DL) approaches, including building Deep Neural Networks (DNN) to detect irony and sarcasm content. However, most of them concentrated on detecting sarcasm in English rather than Arabic content. Especially studies concerning deep neural networks, including convolutional neural networks (CNN) and recurrent neural network (RNN) architectures. This paper investigates
Providing a labeled statements dataset to enhance the trans-compilation-based tools
Nowadays Mobile Applications are a necessity as everyone is depending on them in their everyday tasks. We use them for communication, entertainment, and utilities. Every day new devices are introduced to the market. The diversity in these devices resulted in many platforms like Android and iOS. These different mobile platforms used by different companies and manufacturers made it challenging for mobile developersto build an application or a system that can be deployed on different platforms. Developers will be required to go through multiple development cycles to develop the application for
Pagination
- Previous page ‹‹
- Page 12
- Next page ››
