Breadcrumb
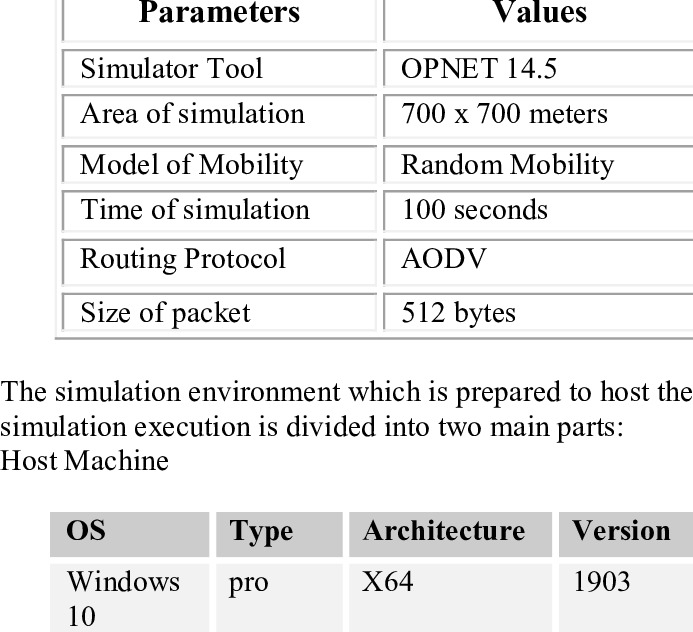
Performance Comparison of AODV and DSDV in Vehicular Ad Hoc Networks
Vehicle Ad-Hoc Networks (VANETs) are a special type of Mobile Ad-Hoc Network (MANETs). In VANETs, a group of vehicles communicates with each other to transfer data without a need for a fixed infrastructure. In this paper, we compare the performance of two routing protocols: Ad-hoc on Demand Distance Vector protocol (AODV) and Destination-Sequenced Distance Vector protocol (DSDV) in VANETs. We measure the reliability of each protocol in the packet delivery. © 2022 IEEE.
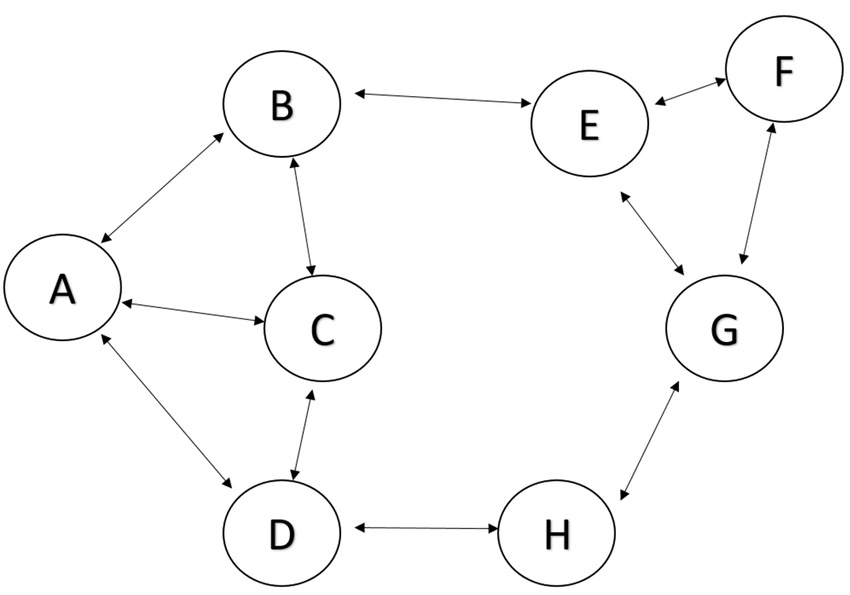
Blackhole Attack effect on MANETs' Performance
Mobile Ad hoc networks (MANETs) facilitate the communication of devices with a limited communication range. A MANET can be described as a decentralized network with a constantly changing topology. This makes it vulnerable to different attacks. The black hole is one of the most dangerous attacks in MANETs. This paper discusses the Blackhole attack in a random mobility environment and analyses its impact on MANETs using several parameters for single and multiple connections. © 2022 IEEE.
On The Arabic Dialects' Identification: Overcoming Challenges of Geographical Similarities Between Arabic dialects and Imbalanced Datasets
Arabic is one of the world's richest languages, with a diverse range of dialects based on geographical origin. In this paper, we present a solution to tackle subtask 1 (Country-level dialect identification) of the Nuanced Arabic Dialect Identification (NADI) shared task 2022 achieving third place with an average macro F1 score between the two test sets of 26.44%. In the preprocessing stage, we removed the most common frequent terms from all sentences across all dialects, and in the modeling step, we employed a hybrid loss function approach that includes Weighted cross entropy loss and Vector
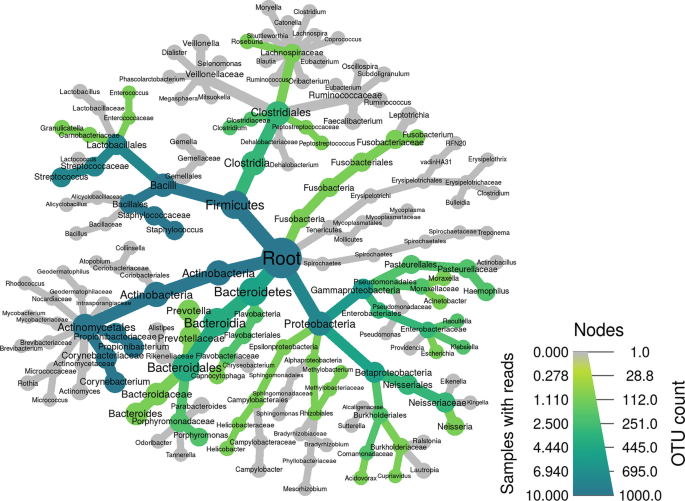
Comprehensive Guideline for Microbiome Analysis Using R
The need for a comprehensive consolidated guide for R packages and tools that are used in microbiome data analysis is significant; thus, we aim to provide a detailed step-by-step dissection of the most used R packages and tools in the field of microbiome data integration and analysis. The guideline aims to be a user-friendly simplification and tutorial on five main packages, namely phyloseq, MegaR, DADA2, Metacoder, and microbiomeExplorer due to their high efficiency and benefit in microbiome data analysis. © 2023, The Author(s), under exclusive license to Springer Science+Business Media, LLC
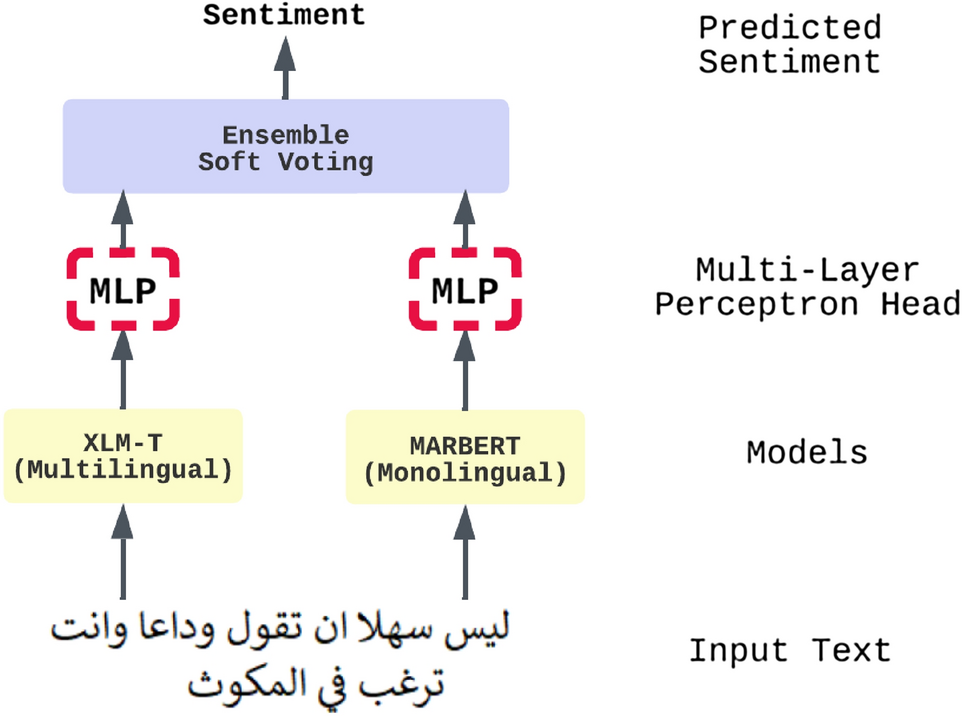
An ensemble transformer-based model for Arabic sentiment analysis
Sentiment analysis is a common and challenging task in natural language processing (NLP). It is a widely studied area of research; it facilitates capturing public opinions about a topic, product, or service. There is much research that tackles English sentiment analysis. However, the research in the Arabic language is behind other high-resource languages. Recently, models such as bidirectional encoder representations from transformers (BERT) and generative pre-trained transformer (GPT) have been widely used in many NLP tasks; it significantly improved performance in NLP tasks, especially
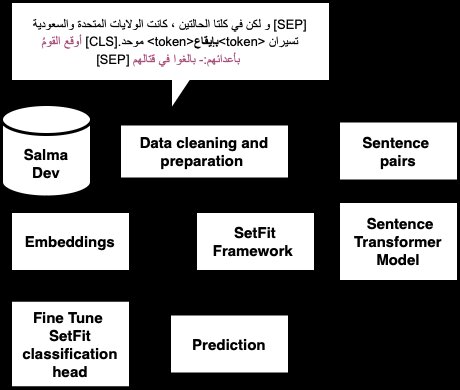
Pirates at ArabicNLU2024: Enhancing Arabic Word Sense Disambiguation using Transformer-Based Approaches
This paper presents a novel approach to Arabic Word Sense Disambiguation (WSD) leveraging transformer-based models to tackle the complexities of the Arabic language. Utilizing the SALMA dataset, we applied several techniques, including Sentence Transformers with Siamese networks and the SetFit framework optimized for few-shot learning. Our experiments, structured around a robust evaluation framework, achieved a promising F1-score of up to 71%, securing second place in the ArabicNLU 2024: The First Arabic Natural Language Understanding Shared Task competition. These results demonstrate the
Unravelling Diabetes-related Pathways Using 16S rRNA Microbiome Data from Human Gut and Nasal Cavity
Type 2 Diabetes (T2D) is a complex chronic illness that affects around 90% of diabetic patients worldwide. Prediabetes is an elementary phase for T2D that is recommended to be early diagnosed to prevent its progression. In this study, we used 16S rRNA data from the gut and nasal cavity of prediabetic and control patients to identify common and exclusive diabetic pathways for each body site. Furthermore, using the Phylogenetic Investigation of Communities by Reconstruction of Unobserved States (PICRUSt) as well as MicobiomeExplorer in the pathway enrichment analysis, we also identified the
From Gestures to Audio: A Dataset Building Approach for Egyptian Sign Language Translation to Arabic Speech
The communication barriers faced by people with disabilities, particularly the deaf or hard of hearing, nonverbal, deaf-mute, and blind have a significant impact on their quality of life and social inclusion. Our research aims to provide real-time translation from sign language to speech and vice versa. The ability to provide real-time speech-to-text and text-to-sign language translation will help alleviate these barriers, improve communication, and increase social inclusivity for this community ensuring they are not left out in conversations and social interactions. A significant amount of
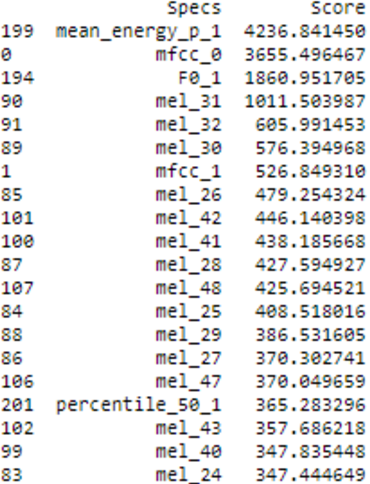
Arabic English Speech Emotion Recognition System
The Speech Emotion Recognition (SER) system is an approach to identify individuals' emotions. This is important for human-machine interface applications and for the emerging Metaverse. This work presents a bilingual Arabic-English speech emotion recognition system based on EYASE and RAVDESS datasets. A novel feature set was composed by using spectral and prosodic parameters to obtain high performance at a low computational cost. Different classification models were applied. These machine learning classifiers are Random Forest, Support Vector Machine, Logistic Regression, Multi-Layer Perceptron
Genomic image representation of human coronavirus sequences for COVID-19 detection
Coronavirus (CoV) disease 2019 (COVID-19) is a severe pandemic affecting millions worldwide. Due to its rapid evolution, researchers have been working on developing diagnostic approaches to suppress its spread. This study presents an effective automated approach based on genomic image processing (GIP) techniques to rapidly detect COVID-19, among other human CoV diseases, with high acceptable accuracy. The GIP technique was applied as follows: first, genomic graphical mapping techniques were used to convert the genome sequences into genomic grayscale images. The frequency chaos game
Pagination
- Previous page ‹‹
- Page 8
- Next page ››
